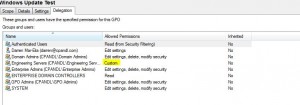
One of the challenges of the GPMC’s reporting is that it is not easy to find GPOs that have had Deny ACEs (Access Control Entries) set on their delegation. Deny ACEs are typically used to deny a particular user, computer or group from applying a GPO. I always recommend that they’re used on an exception basis, for the very reason that they are hard to spot after the fact and can cause increased complexity in your Group Policy deployments. Deny ACEs don’t appear in the “Scope” tab for a GPO, under the Security Filtering section. And they don’t even really appear under the “Delegation” tab. Instead what you see is a trustee (i.e. user, group or computer) listed with a permission of “Custom” (see below).
Unfortunately, “custom” doesn’t guarantee that it’s a deny ACE, which means that you have to drill into it further using the Advanced button in the lower right of the delegation tab, to ensure that it is, indeed a Deny ACE. The effects of an unwanted or unknown Deny ACE on a GPO, perhaps set by someone who is no longer managing your GPOs long ago, is that it can prevent GPO from processing in ways that are not obvious (at least on the surface). Usually you spend hours trying to troubleshoot why a GPO setting isn’t working for a given computer or user, only to run an RSoP report and discover that the GPO appears in the “Denied GPOs” list as “Access Denied (Security Filtering)”. You look at the Delegation and Scope tabs again in GPMC, scratch your head and wonder what’s up!
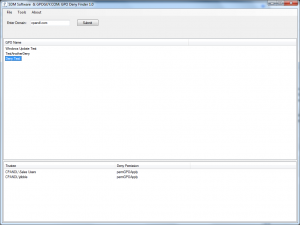
Well, after spending enough time over the years with this issue, I wrote a little utility that helps shine a light on this problem once and for all. It’s called the GPO Deny Finder, and it’s job is simple. When it starts up, you can enter an AD domain name (or it finds your current domain). You press the “Submit” button and away it goes, trolling your domain GPOs for Deny ACEs. Once it find a GPO that has one, it adds it to the list. When it’s done, you can select a given GPO, and it will show you what Deny ACEs exist for that GPO, as seen below:
You can also export the list of GPOs and their Deny ACEs to CSV if you need to document them further. That’s all there is to the GPO Deny Finder. Simple but powerful! You can download the tool from our GPOGUY.COM Free Tools Library. I’ve also recorded a quick video that you can watch to see how to use the tool.
Enjoy!
Darren