If any of you were at Microsoft’s Ignite conference last week, and caught the session I participated in around Group Policy, you might have heard me talk about an exciting new piece of technology related to PowerShell Desired State Configuration that we were releasing soon. Well, I’m happy to announce that it’s here! So, what is it?
Push, Pull and…GP?
If you’ve followed my blog over the past couple of years, you know that I’ve become a big fan of PowerShell’s Desired State Configuration (DSC) technology, which provides a declarative language extension to PowerShell v4 and above that allows you to describe and then deploy configurations to Windows Servers (primarily) as well as Windows desktops. DSC provides two “transports” to get configuration to a system. The first is called “push” and allows you, as the administrator, to interactively send configuration documents to one or more target nodes. That model, of course, relies on the targets being up and available at the time you push the configuration, but it’s a great method for doing “right-now” deployments of configuration via DSC. The other built-in method of deploying DSC is called “pull”, where client systems pull DSC documents from specially deployed pull servers, either over HTTP web services or SMB file shares.
This is all great for a number of reasons. For one, DSC doesn’t required AD in order to target and deploy configurations. It is also “firewall-friendly” when it comes to deploying configuration over the Internet (i.e. in the cloud). That said, there are some challenges that folks have with respect to deploying DSC today. Some of these I’ve already talked about in other blog posts, but among them:
- Deploying a DSC Pull Server is currently not super-intuitive and somewhat limited in terms of securing configuration documents
- Targeting of DSC documents is rudimentary and not at all dynamic (IOW, you have to pre-decide which DSC document is going to which Windows device during the authoring phase)
- Sometimes you’d like for DSC document deployment to map to your AD structure. This is not altogether easy today
These “limitations” end up depending upon how you’re using DSC (e.g. they may not be terribly critical for a DevOps style deployment of Web Server applications) but we think DSC can and should be used for much more than that. So we decided to merge the best of DSC with the best of Group Policy into a new DSC Client Side Extension for Group Policy–a freeware utility that we’re making available to folks to help them leverage more of DSC in their GP environments.
“DSC CSE”–Say that 3 times fast!
So, what is the DSC CSE for? Well, let’s think about what DSC is good for today:
DSC
- Optimized for Windows Server configurations
- Really infinitely extensible in terms of what you can configure, which a large and growing body of community resources being developed
- Flexible authoring model for creating configuration documents (i.e. can be done via script rather than through hard-coded UIs)
- DSC client–the Local Configuration Manager–provides idempotent check and apply logic to keep configurations consistent and compliant over time, in a more robust way that the GP engine currently does. This is ideal for scenarios like security compliance!
And that’s to name just a few of it’s advantages. On the other hand, GP provides:
Group Policy
- Optimized for Windows client configurations
- Extensible, but requires complex C++-based CSEs an MMC snap-ins
- Scalable, and secure delivery of configuration instructions within an AD-domain environment
- Flexible, dynamic, delivery-time targeting using AD or other criteria (e.g. OU, security groups, WMI etc.)
Given all that, it’s logical to assume that GP might benefit from DSC’s infinite extensibility and more robust “compliance engine” when it comes to setting and keeping a particular configuration–especially security or application configuration. In addition, DSC brings a strength on the server-side of configuration that GP traditionally has not had.
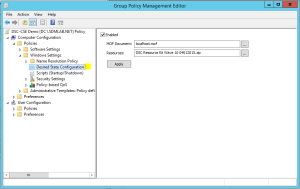
All that is to say that what we are delivering today is a GP CSE and accompanying GP Editor MMC snap-in (see below) that extends Group Policy to allow you to assign DSC documents to GPOs, and then target those DSC documents using GP’s flexible targeting mechanisms. At the client receiving those DSC documents, the CSE hands off the DSC document to the DSC Local Configuration Manager (LCM), which processes them just as DSC would do natively. So you get all the benefits of GP as a transport, and all the strengths of DSC as an extensible configuration engine–the best of both worlds!
So go download the DSC CSE now and please provide us feedback, either through the GPTalk forums or via support@sdmsoftware.com. I look forward to hearing what more you’d like to see in the CSE!
Thanks,
Darren


hey dcs cse is still working or not? I did downloaded and tested oiut, but it did not worj the way which Pull server performs.
any idea?
Hard to say given that little information. Did it process any of the mof file?
hey I just tried to download it again, but it failed
404: Page Not Found
any idea?
You can download it from here: https://s3.amazonaws.com/sdmsoftware.com/dl/DSC+GP+Extension+Setup+1.06.zip